Nearly four years following the introduction of a security feature known as Lockdown Mode, Apple claims it has not encountered a situation where an individual’s device was compromised with these enhanced security measures activated.
“To our knowledge, there have been no successful mercenary spyware incursions on devices enabled with Lockdown Mode,” stated Apple spokesperson Sarah O’Rourke to TechCrunch on Friday.
This is the latest confirmation from the tech behemoth that Apple devices operating under Lockdown Mode can endure government spyware intrusions, having first made this assertion a year after the launch of the security feature.
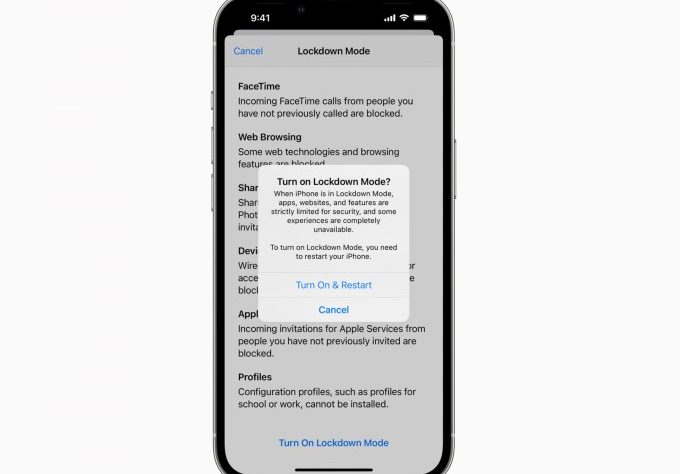
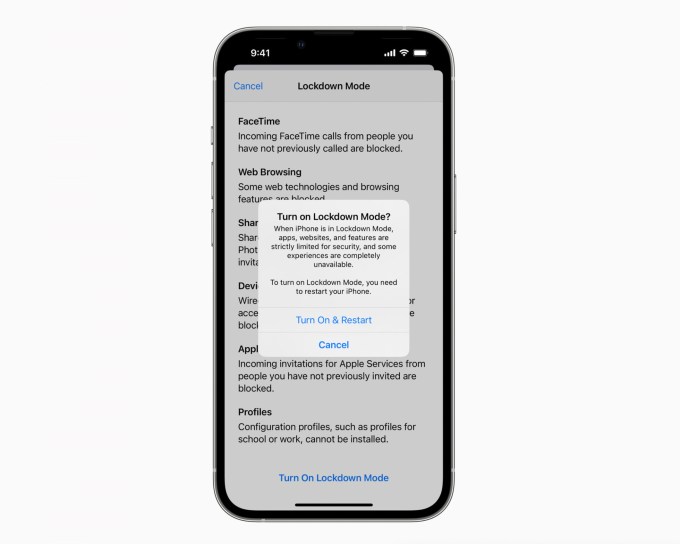
In 2022, Apple introduced Lockdown Mode, an opt-in set of security measures that disables certain features on iPhones and other Apple products that are frequently exploited for hacking targets using spyware. Apple specifically developed this security mode to aid vulnerable customers in shielding themselves against the dangers presented by government spyware produced by firms like Intellexa, NSO Group, and Paragon Solutions.
In recent times, Apple has acknowledged that its clientele can fall prey to spyware and has adopted a more assertive approach to inform customers who have been targeted.
Apple has dispatched multiple notifications to users across more than 150 nations, notifying them that they could have been compromised by spyware, highlighting the level of insight the company now possesses regarding these types of attacks. Although Apple has never disclosed how many users have been informed, it’s reasonable to conclude that the numbers are in the dozens, if not more.
Donncha Ó Cearbhaill, the leader of the security lab at Amnesty International, where he has examined numerous spyware incidents, mentioned that he and his team “have not observed any proof of an iPhone being successfully infiltrated by mercenary spyware while Lockdown Mode was active during the attack.”
Digital rights groups such as Amnesty International and the University of Toronto’s Citizen Lab have cataloged various successful assaults on iPhone users, none of which reported a breach of Lockdown Mode. In a minimum of two instances, Citizen Lab researchers have publicly stated that they witnessed Lockdown Mode effectively thwart spyware attacks, one involving NSO’s Pegasus and another with Predator spyware, developed by a company that is now under Intellexa.
In at least one recorded incident of spyware targeting iPhones, security analysts at Google indicated that the spyware would abandon its attempt to infect the target if Lockdown Mode was detected, likely as a method to avoid being noticed.
Patrick Wardle, a cybersecurity expert focused on Apple and a critic, asserts that Lockdown Mode is a vital feature that complicates the task for spyware creators aiming to target Apple users.
“It can be confidently said that Lockdown Mode represents one of the most rigorous consumer-facing hardening features ever implemented,” he conveyed to TechCrunch.
Contact Us
Do you have further information regarding spyware attacks or the manufacturers of spyware? From a non-work device, you can securely reach Lorenzo Franceschi-Bicchierai on Signal at +1 917 257 1382, or via Telegram, Keybase, and Wire @lorenzofb, or by email.
Wardle clarified that by “minimizing the attack surface,” Lockdown Mode eliminates various strategies typically employed to exploit the iPhone, compelling spyware developers to resort to more sophisticated and costly methodologies.
“It neutralizes entire delivery mechanisms/exploit classes,” he added, “as it restricts most message attachment formats and limits WebKit capabilities. This represents a substantial decrease in the remotely accessible attack surface, particularly concerning zero-click exploit chains,” referring to intrusions that can target individuals over the internet without requiring any action from the victim.
It’s plausible that Lockdown Mode has been circumvented, and neither Apple nor independent analysts have detected the breach. However, considering that Apple usually maintains a publicly reserved stance, its latest proclamation signifies a notable point for Lockdown Mode.
I have utilized Lockdown Mode for several years, and I seldom think about it — except when notifications appear that can sometimes be perplexing. Some features that have been disabled necessitate an additional step, such as copying and pasting links from text messages into your browser. That’s why I, along with several digital security professionals, advise anyone concerned about being targeted by spyware or cyber assaults to enable Lockdown Mode.