This incident is one of those real-life situations from Silicon Valley that could easily be part of an HBO parody. This week, a truly dreadful piece of malware was found in an open source initiative created by LiteLLM, a graduate of Y Combinator.
LiteLLM allows developers to effortlessly access numerous AI models and offers functionalities like expense management. It has become a significant success, reportedly downloaded up to 3.4 million times daily, according to Snyk, one of the multiple security analysts observing the situation. The project had garnered 40K stars on GitHub and thousands of forks (those who utilized it as a foundation to modify and personalize it).
The malware was identified, recorded, and made public by research scientist Callum McMahon from FutureSearch, a company providing AI agents for online research. The malware infiltrated through a “dependency,” which refers to other open source software that LiteLLM depended on. It subsequently stole the login information of everything it encountered. With those credentials, the malware accessed more open source packages and accounts to gather additional credentials, and so forth.
The malware caused McMahon’s computer to crash after he downloaded LiteLLM. This event led him to explore and uncover it. Ironically, a flaw in the malware led his device to malfunction. Because of the careless design of that malicious code, both he and renowned AI researcher Andrej Karpathy concluded it must have been coded without proper care.
The LiteLLM team has been tirelessly addressing the issue this week, and the good news is that it was detected relatively quickly, probably within hours.
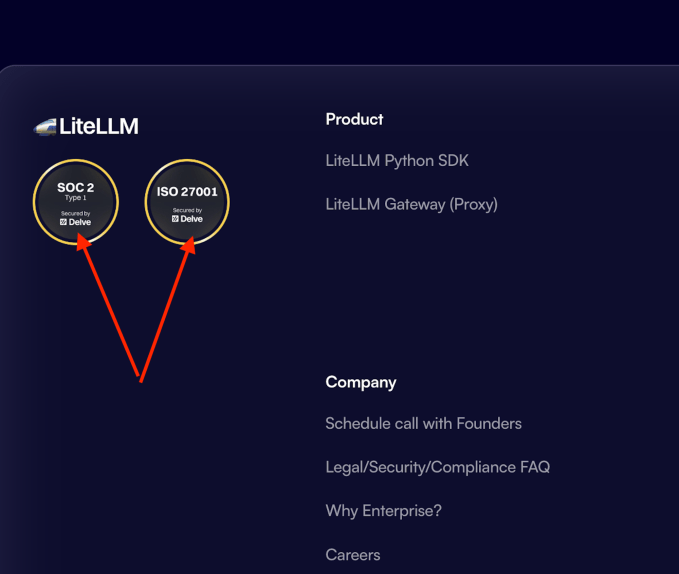
There’s an additional aspect to this story that users on X are eagerly discussing. As of March 25, when we checked, LiteLLM was still proudly advertising on its site that it has achieved two significant security compliance certifications, SOC2 and ISO 27001.
However, it utilized a startup named Delve for those certifications.
Techcrunch event
San Francisco, CA
|
October 13-15, 2026
Delve is the Y Combinator AI-powered compliance startup that has faced accusations of deceiving its clients regarding their actual compliance status by allegedly creating fabricated data and employing auditors who merely approve reports. Delve has rejected these claims.
There is an aspect of nuance here that merits comprehension. Such certifications are meant to demonstrate that a company has robust security protocols established to reduce the likelihood of occurrences like this. Certifications do not inherently safeguard a company, like LiteLLM, from malware attacks. While SOC 2 is expected to address policies regarding software dependencies, malware can still infiltrate.
Nevertheless, as engineer Gergely Orosz remarked on X when he noticed individuals mocking it online, “Oh no, I thought this WAS a joke. … but no, LiteLLM *really* was ‘Secured by Delve.’”
Regarding LiteLLM, CEO Krrish Dholakia refrained from commenting on the use of Delve. He remains occupied rectifying the unfortunate situation from being a target of the attack.
“Our immediate focus is the ongoing investigation with Mandiant. We are dedicated to sharing the technical insights gained with the developer community once our forensic review is concluded,” he informed TechCrunch.
