Activists have taken credit for disrupting the publicly accessible infrastructure of the widely-used Linux operating system distribution Ubuntu, along with Canonical, the firm that develops and maintains the platform. The assault commenced on Thursday, impacting services essential for Ubuntu users.
“Canonical’s online framework is experiencing a prolonged, international attack and we are striving to resolve the situation. We will share further updates through our official channels as soon as feasible,” the company stated on its website.
The activists are thought to have executed a distributed denial-of-service, or DDoS, which is a basic yet frequently effective strategy of bombarding a target with excessive traffic until it becomes overwhelmed or crashes.
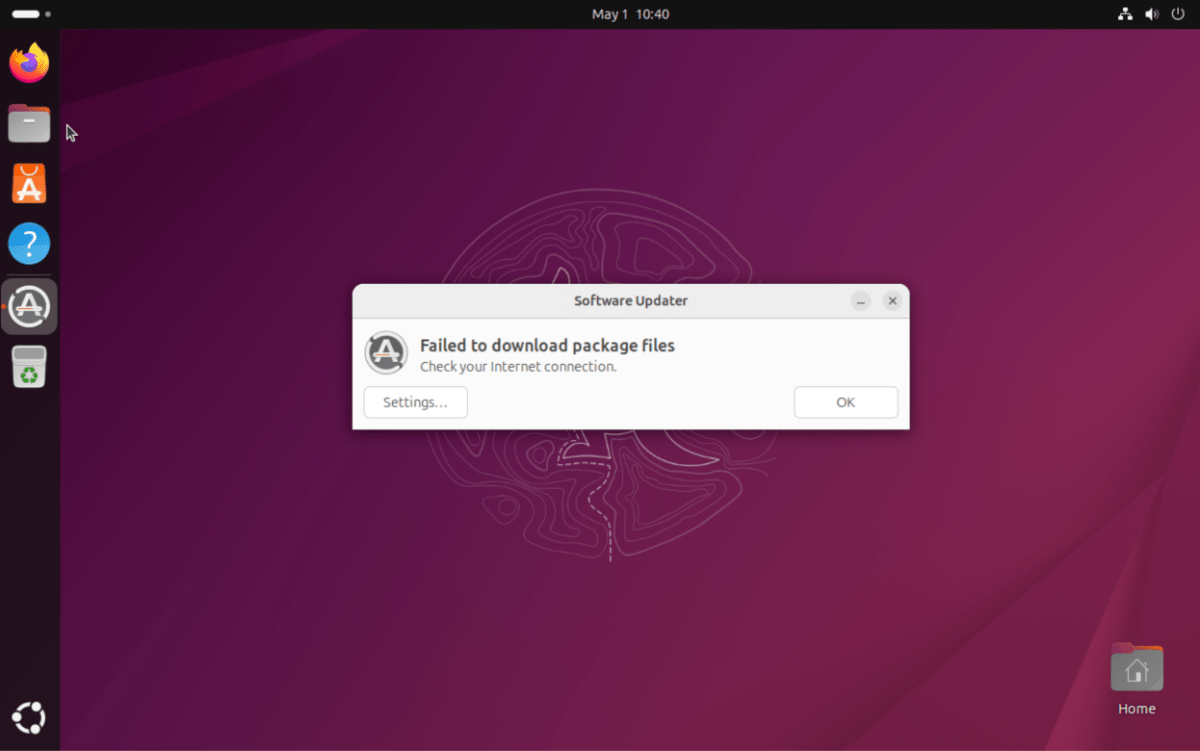
Ubuntu developers have been talking about the incident on an unofficial Ubuntu community forum, asserting that the attack impacts Ubuntu’s security API, as well as multiple Ubuntu and Canonical websites. Based on a discussion on a threat intelligence forum, the DDoS assault has also rendered it impossible for users to update or install Ubuntu. TechCrunch confirmed that updates failed to install on a test device operating Ubuntu.
At the time of this writing, the outage has persisted for approximately 20 hours.
When reached for comment, Canonical representative Lelanie de Roubaix reiterated the information presented on the company’s website.
Activists identifying themselves as The Islamic Cyber Resistance in Iraq 313 Team asserted on their Telegram channel that they are responsible for the DDoS attack.
Techcrunch event
San Francisco, CA
|
October 13-15, 2026
The attackers claimed to be utilizing Beamed, a DDoS-for-hire platform. Such services, sometimes referred to as booters or stressers, enable anyone to pay for launching DDoS assaults, regardless of their technical expertise or the required infrastructure to inundate targets with fraudulent traffic. The DDoS-for-hire service in this situation purports to support attacks exceeding 3.5 Tbps, which is approximately half the bandwidth of a cyber assault that Cloudflare labeled last year the “largest DDoS attack ever documented.”
For years, agencies like the FBI and Europol have been engaged in a continuous effort to combat these services, dismantling and seizing domains, and occasionally apprehending those behind them.
This story was revised to incorporate Canonical’s response.
When you purchase through links in our articles, we may earn a small commission. This doesn’t affect our editorial independence.