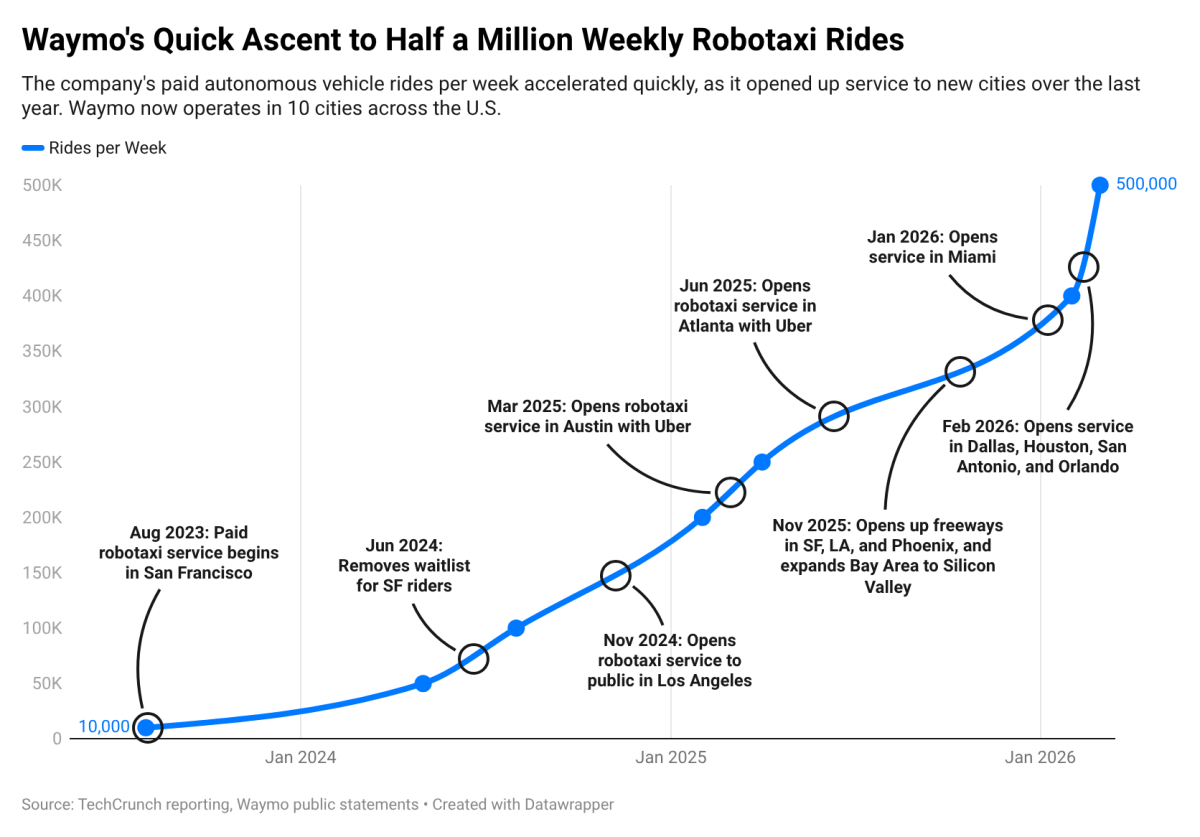
Waymo is currently offering 500,000 paid robotaxi rides weekly across 10 U.S. cities, as stated by the company in a post on X this week. This impressive figure highlights the accelerated commercial growth of the Alphabet-owned firm. However, it is Waymo’s expansion in ridership and markets that presents a more intriguing narrative.
In under two years, the company’s average weekly paid robotaxi rides have surged tenfold, increasing from 50,000 in May 2024 to 500,000 today. During the same two-year period, Waymo has broadened its presence from its original markets of Phoenix, San Francisco, and Los Angeles to include Austin, Atlanta, Miami, Dallas, Houston, San Antonio, and Orlando. All seven of these Sun Belt cities were added in just the past year.
Waymo’s robotaxi fleet has also expanded, although the company has been reticent about the specifics and infrequently provides updates. Information shared in December 2025 with the National Highway Traffic Safety Administration (NHTSA) indicated the company operated 3,067 robotaxis equipped with its fifth-generation self-driving system. The company continues to use that “over 3,000” fleet count today. This may soon change with the rollout of its sixth-generation self-driving system, set to launch on the Zeekr minivan, dubbed Ojai, and the Hyundai Ioniq 5.
The consistent fleet figure of around 3,000, coupled with the rising number of weekly paid rides, implies that Waymo is maximizing efficiencies with each robotaxi. This utilization metric is especially crucial, as empty Waymo vehicles wandering around San Francisco or other locations do not generate revenue and can exacerbate congestion.
However, this growth comes with hurdles. Waymo has faced increased scrutiny recently from both the public and regulatory bodies. For example, the NHTSA and the National Transportation Safety Board are investigating the misconduct of Waymo robotaxis around school buses. Simultaneously, San Francisco city officials have expressed concerns regarding how the company manages robotaxis that become stuck, including instances where Waymo has employed police and firefighters to assist in clearing its vehicles.
Waymo’s ridership numbers still represent a small fraction of Uber’s human-driven ride-hailing operations. According to securities filings, Uber completed approximately 13.5 billion trips in 2025, encompassing both ride-hailing and delivery services. The closest comparable ride-hail statistic was disclosed during Uber’s August 2024 earnings call, where the company reported completing over 1 million mobility trips per hour.
In essence, Waymo has not yet begun to significantly challenge Uber.
Techcrunch event
San Francisco, CA
|
October 13-15, 2026
Nonetheless, with each passing month, the company’s lead in robotaxi rides continues to widen.
Several firms are competing for a piece of the robotaxi market, though many have not yet introduced a fully autonomous ride-hailing service that charges fees. While there are some Chinese robotaxi companies like Pony.ai and WeRide that do charge for rides, none operate within the United States.
Tesla initiated a paid robotaxi service in Austin in January, and although CEO Elon Musk has claimed the company is close to a fully autonomous ride-hailing service in California, it currently lacks the necessary permits. Other companies, including Avride, Hyundai-owned Motional, and Zoox, are all striving to launch paid robotaxi services in various regions by the year’s end.
All of them have considerable ground to cover.