A seasoned cybersecurity leader who prosecutors claimed “betrayed” the United States is set to serve a minimum of seven years in prison after admitting guilt to the theft and sale of hacking and surveillance tools to a Russian company.
Peter Williams, a former executive at U.S. defense contractor L3Harris, received a sentence of 87 months on Tuesday for disclosing trade secrets from his former employer in exchange for $1.3 million in cryptocurrency between 2022 and 2025. He sold these exploits to Operation Zero, described by the U.S. government as “one of the most notorious exploit brokers globally.”
The conviction of Williams is part of one of the most notable breaches of sensitive, Western-developed hacking tools in recent times. Even with the conclusion of the case, many questions remain unanswered.
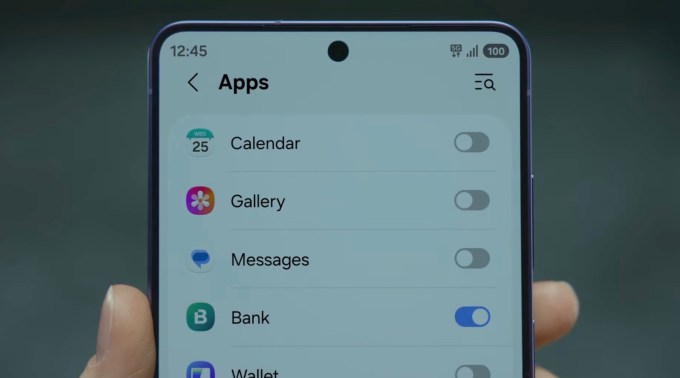
Williams, a 39-year-old Australian national living in Washington, D.C., was the general manager of Trenchant, the segment of L3Harris responsible for creating hacking and surveillance instruments for the U.S. government and its key intelligence partners globally. Prosecutors suggest Williams exploited his “full access” to the company’s secure networks to transfer hacking tools to a portable hard drive, and subsequently to his personal computer. He communicated with Operation Zero using an alias, making it uncertain whether they knew his true identity.
Trenchant comprises a team of hackers and bug hunters who deeply analyze popular software produced by companies like Google and Apple, pinpointing vulnerabilities in vast lines of code, then inventing methods to convert these vulnerabilities into usable exploits that can reliably compromise those products. These tools are commonly referred to as zero-day exploits due to their exploitation of software defects unknown to the developer, often valued in the millions.
The U.S. Department of Justice claimed that the hacking tools sold by Williams could have enabled their users to “potentially access millions of computers and devices globally.”
For several months, I had been in conversations with sources and covering Williams’ situation before news of his arrest circulated. However, the information I gathered was fragmented and at times inconsistent. I had heard of an arrest, but due to the clandestine nature involved in exploit development, establishing the facts would prove difficult.
Contact Us
If you possess further insights into this case and the supposed leak of Trenchant hacking tools, you can reach Lorenzo Franceschi-Bicchierai securely on Signal at +1 917 257 1382 from a non-work device, or through Telegram, Keybase, and Wire @lorenzofb, or via email.
Initially, when I learned of Williams, I wasn’t certain I had even accurately identified him. At that time, his story circulated as a rumor within the confidential networks of zero-day exploit developers, sellers, and individuals linked to the intelligence sector.
I heard varying names, perhaps John, or maybe Duggan? Or all the various ways to spell that in English.
Some of the early rumors were conflicting. It seemed he had taken zero-days from Trenchant and sold them to Russia, or possibly to another adversary of the United States and its allies, like North Korea or China?
It took several weeks just to verify that indeed there was an individual who matched that description. (It became apparent that Williams’ middle name is John, and Doogie is his hacker alias.)
Over time, as the reporting proceeded, clarity began to emerge.
The Russian connection
As I initially disclosed in October, Trenchant terminated an employee after Williams, who was still leading Trenchant at that point, accused him of stealing and leaking Chrome zero-days. This situation grew even more intriguing when the employee informed me that after his dismissal, Apple alerted him that someone had targeted his personal iPhone.
What I uncovered was merely the beginning. I had gathered more from my sources, yet we were still piecing the narrative together.
Shortly thereafter, prosecutors formally accused a man named Peter Williams of stealing trade secrets, which first appeared in the U.S. public court documentation. The initial court filing confirmed that the purchaser of these secrets was a buyer based in Russia.
However, there was no direct mention of L3Harris or Trenchant, nor was it established that the trade secrets that Williams pilfered were zero-days. Importantly, we still could not definitively verify whether it was the same Peter Williams thought to possess access to highly sensitive exploits as Trenchant’s head, or if this was just an unfortunate case of mistaken identity.
We still weren’t there.
On a hunch, with nothing to lose, we reached out to the Department of Justice to inquire if they would verify that the individual named in the document was indeed Peter Williams, the former head of L3Harris Trenchant. A spokesperson confirmed.
At last, the story became public. A week later, Williams entered a guilty plea.
When I first learned about his situation, I trusted my sources, yet I remained doubtful. Why would someone like Williams engage in the actions described by the rumors? Yet he did, allegedly for financial gain, which he utilized to purchase a home, jewelry, and luxury watches.
This marked a significant fall from grace for Williams, once considered a talented and brilliant hacker, and particularly for someone who had previously served at Australia’s foremost foreign intelligence agency and in the nation’s military.

What happened to the stolen exploits?
We still lack specific details regarding which exploits and hacking tools Williams appropriated and distributed. Trenchant projected a loss of $35 million, according to court records. However, Williams’ legal team indicated that the pilfered tools were not designated as classified government secrets.
We can deduce certain insights based on the case’s circumstances.
Since the Justice Department stated that the stolen tools could be utilized to infiltrate “millions of computers and devices,” it is plausible that they pertain to zero-days in widely-used consumer software such as Android devices, Apple’s iPhones and iPads, and various web browsers.
There is some evidence suggesting this direction. At a hearing last year, prosecutors recited a post from Operation Zero on X, as per independent cybersecurity journalist Kim Zetter, who attended the hearing.
“Due to high demand on the market, we’re increasing payouts for top-tier mobile exploits,” stated the post, explicitly mentioning Android and iOS. “As always, the end user is a non-NATO country.”
Operation Zero offers significant sums for insights into security vulnerabilities in Android devices and iPhones, messaging applications like Telegram, as well as various software, such as Microsoft Windows, and hardware vendors, including multiple brands of servers and routers.
Operation Zero alleges cooperation with the Russian government. When Williams sold the exploits to the Russian broker, Putin’s extensive invasion of Ukraine was already active.
On the day Williams was sentenced, the U.S. Treasury announced sanctions against Operation Zero and its founder Sergey Zelenyuk, labeling the organization a national security hazard. This was the first government confirmation that Williams had sold the exploits to Operation Zero.
In its statement, the Treasury noted that the broker “sold those stolen tools to at least one unauthorized user.” At this juncture, we remain unaware of the identity of this user, who could be a foreign intelligence agency or possibly a ransomware group, as the Treasury also sanctioned Oleg Vyacheslavovich Kucherov, an alleged member of the Trickbot gang, who reportedly worked with Operation Zero.
In a court filing, prosecutors indicated that L3Harris managed to determine that “an unauthorized vendor was selling a component” of one of the stolen trade secrets “by matching company-specific vendor data found on a stolen component.”
Prosecutors also claimed that Williams “recognized code he authored and sold” to Operation Zero “being used by a South Korean broker,” further implying that both L3Harris and prosecutors are aware of which tools were pilfered and sold to Operation Zero.
Another question that remains is: Did anyone, whether the U.S. government or L3Harris, notify Apple, Google, or whichever technology company’s products were compromised by the zero-day vulnerabilities, now that the exploits had leaked?
Any organization or developer would want to ascertain that someone could have employed (or could still utilize) a zero-day against their users and clients to patch the flaws as quickly as possible. At this point, the zero-days are of no benefit to L3Harris and its government clients.
Inquiries to Apple and Google yielded no responses. L3Harris also did not provide a reply.
Who hacked the scapegoat, and why?
Then there is the enigma of the scapegoat, who was dismissed following Williams’ allegations of theft and leaking of code.
During sentencing, Justice Department prosecutors affirmed that the employee was terminated, stating that Williams “stood idly by while another employee of the company was essentially blamed for [his] own actions.” In defense, Williams’ attorney countered prosecutors by asserting that the former employee “was dismissed for misconduct,” referencing claims of dual-employment and improper management of the company’s intellectual property.
According to a court document filed by Williams’ legal representatives, in the course of the L3Harris internal investigation, the company placed the employee on leave, confiscated his devices, sent them to the U.S., and “offered them to the FBI.”
In response to requests for comments, an unnamed FBI spokesperson stated that the bureau had nothing further to contribute aside from the Justice Department’s press release.
After his termination, the employee, who we’re identifying as Jay Gibson, received a warning from Apple stating that his personal iPhone was targeted “with a mercenary spyware attack.”
Apple issues these alerts to users it suspects are targeted by attacks utilizing tools produced by firms like NSO Group or Intellexa.
Who attempted to hack Gibson? He received the alert on March 5, 2025, more than six months after the FBI investigation had commenced. The FBI “regularly interacted with [Williams] in late 2024 through the summer of 2025,” according to a court document.
Considering the nature of the leaked tools, it is reasonable to speculate that the FBI, or possibly even a U.S. intelligence agency, might have targeted Gibson as part of the inquiry into Williams’ leaks. However, we cannot say for certain, and it’s possible that neither the public nor Gibson will ever learn the truth.
Updated to clarify the 22nd paragraph attributing the tools’ lack of classification to Williams’ attorneys.